GCP Shared VPC IDS IPS
Originally
ADR-0030_GCP_Shared_VPC_IDS-IPS (v6) · Source on Confluence ↗GCP IDS/IPS Architecture
Status: Accepted
Deciders: ryan.cullison@droneup.com, sybil.melton@droneup.com, eric.brookman@droneup.com
Date: May 4, 2023
Technical Story
Find an IDS/IPS solution for [Shared VPC][1] in order to meet NIST 800-53 compliance, as well as improve security posture with higher conditions of diligence, integrity, trust, and threat prevention.
Context and Problem Statement
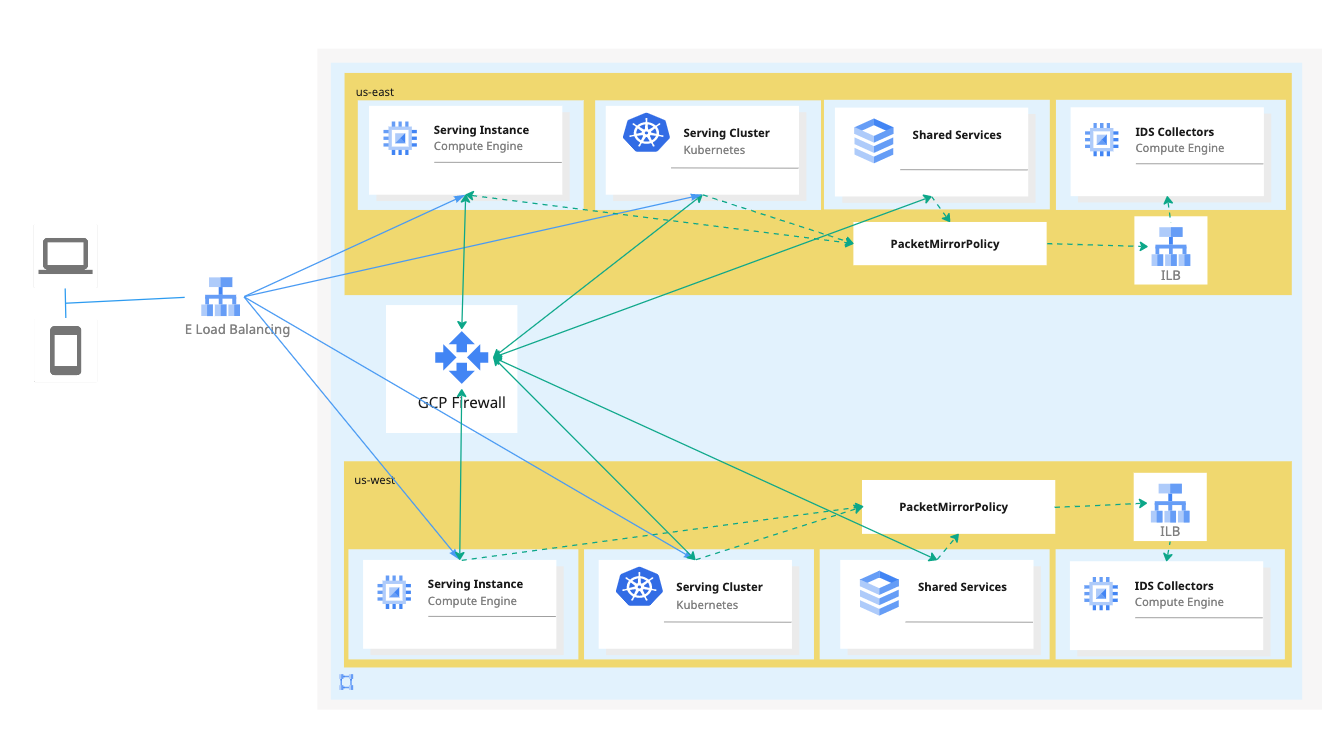
- A comprehensive, advanced GCP security approach that secures all flows, ingress, egress, and east-west.
- Segmentation combined with content inspection to prevent lateral movement of attacks.
- Preventing connections to malicious sites and command-and-control (C2), and stopping exfiltration of sensitive information (DLP).
As discussed in [ADR17: GCP Network Architecture](confluence-title://PE/ADR17: GCP Network Architecture), Shared VPC will be the network architecture. Host project contains GCP firewall policy, possible packet mirroring for IDS, and/or inline IPS/NGFW appliances as required.
| Network Security Function | Ingress | Egress | East-West |
|---|---|---|---|
| Intrusion Detection (IDS) | ✔ Packet mirroring policy on Cloud Firewall ✔ inline appliance | ✔ Packet mirroring policy on Cloud Firewall ✔ inline appliance | ✔ Packet mirroring policy on Cloud Firewall |
| Intrusion Prevention (IPS) | ✔ inline appliance | ✔ inline appliance | ✘ Single shared VPC – Cannot force subnet to subnet traffic (same VPC) to security appliance. ✔ Multiple Shared VPCs - requires inline appliance between VPC peerings |
Decision Drivers
- NIST 800-53 compliance
- Scalability
- Ease of management
- Ease of deployment
Considered Options
Agent-based IDS
Endpoint Detection Response (EDR) continuously detecting unexpected behavior, configuration changes, intrusions, and data theft in real-time.
Can be combined with host based firewall or Kubernetes network policy automation to respond to threats
Any agent will increase load on resources, unknown application impact
May not block malicious network traffic alone
Any agent will have long implementation timeline for testing and monitoring before transitioning to secure blocking state